The Hidden Risk in Plain Sight: Why Signatory Governance Must Be a Board-Level Priority
What Is Signatory Governance?
Signatory governance is the set of policies, controls, and systems that determine who can legally bind an organization through signing authority — and how that authority is granted, maintained, and revoked over time.
Definition: Signatory governance encompasses the end-to-end management of authorized signatory lists, including role-based authority assignment, lifecycle updates triggered by personnel changes, recertification processes, distribution to counterparties and banking partners, and audit-trail maintenance. It is a subset of the broader delegation of authority framework, focused specifically on who has the right to execute commitments on behalf of the organization.
Despite its importance, signatory governance remains one of the most under-managed governance functions in most enterprises. Most organizations still manage signatory authority through manual, document-based processes that persist long after other governance functions have been digitized. The EY and Society for Corporate Governance 2025 survey of 222 governance professionals found that 29% of organizations rate their delegation of authority framework as less than effective, and only 14% use a dedicated IT system to manage it — the rest rely on intranet sites, shared drives, and spreadsheets.
These numbers reveal a governance gap hiding in plain sight. Signatory authority is the mechanism that gives legal force to organizational decisions — contracts, banking instructions, regulatory filings, board resolutions — yet the tools and processes that govern it often lag a generation behind other compliance and risk management capabilities.
Why Signatory Governance Belongs on the Board Agenda
Signatory governance failures are not administrative inconveniences — they are board-level risks with financial, legal, regulatory, and reputational consequences that materialize without warning when control gaps go undetected.
The connection between weak authority controls and financial loss is well-documented. The Association of Certified Fraud Examiners (ACFE) 2024 Report to the Nations found that organizations lose an estimated 5% of annual revenue to fraud, with a median loss of $145,000 per case. More critically, 51% of occupational fraud losses stem from absent or overridden internal controls — the exact conditions that poorly governed signatory lists create. When a departed employee retains signing rights on a bank account, or when authority thresholds go unreviewed after a restructuring, the organization is exposed to precisely the control gaps that enable fraud.
Regulatory frameworks reinforce the urgency. SOX Section 302 requires CEO and CFO certification of internal controls, which includes the authority framework governing financial commitments. The UK Corporate Governance Code mandates that boards maintain sound risk management and internal control systems. The EU’s Corporate Sustainability Reporting Directive (CSRD) extends governance disclosure requirements that touch delegation and authority structures. For organizations subject to SOX and internal control requirements, signatory governance is not optional — it is an auditable control that examiners test.
Ten Signatory Governance Challenges Boards Cannot Ignore
The ten challenges below represent the most common and consequential signatory governance failures, mapped to their primary risk dimensions and the board-level controls required to mitigate each.
- Manual processes invite error and delay. Spreadsheet-based signatory lists are difficult to maintain accurately, especially during periods of organizational change. A single role change can require updates across multiple lists, banking mandates, and counterparty records — each typically actioned by a different team, on a different cadence, with no single record of truth. The lag between a personnel event and complete propagation of the update is the window in which the organization operates with inaccurate authority records.
- Global compliance adds complexity. Different jurisdictions impose different delegation requirements, signing formalities, and documentation standards. A signatory authority valid under English law may not satisfy requirements under local civil law jurisdictions, creating compliance gaps that manual processes cannot systematically track.
- Audits are slowed by poor documentation. When auditors request evidence of who held signing authority at a specific point in time, organizations relying on shared drives and email-based distribution often cannot reconstruct the historical state. This creates audit findings, extends engagement timelines, and signals weak governance to regulators.
- Workforce changes leave gaps in authority. Employee departures, role changes, and reorganizations all require signatory list updates. Delays in revoking authority from departed employees create the conditions for unauthorized transactions and fraud. Learn more in our guide to preventing unauthorized signatures.
- Decentralization undermines control. When individual departments, entities, or regional offices each maintain their own signatory records, the organization loses its ability to answer a fundamental governance question: who can commit us, and at what limits? Siloed management produces inconsistent standards and duplicated or conflicting authority grants.
- Limited visibility breeds blind spots. Executives and board members often cannot answer basic questions about the current state of signing authority across the organization. This lack of visibility means that authority drift — the gradual misalignment between policy intent and operational reality — goes undetected until an incident forces discovery. Understanding what a well-maintained authorized signatory list should contain is the first step toward closing this gap.
- Disconnection from the delegation of authority framework. Signatory rights (who can sign) must align with approval authority (who can approve). When these two layers operate independently, an organization can find itself in a position where someone has signing authority for commitments they were never authorized to approve — or vice versa. The alignment between delegations and signature authority is a governance requirement that manual processes struggle to enforce.
- Legal ambiguity increases exposure. Evolving regulations — from the EU AI Act’s human oversight requirements to updated SOX modernization guidance — create new authority governance obligations that static, document-based processes cannot accommodate without manual intervention and risk of oversight.
- Signatory data faces cybersecurity threats. Authorized signatory lists contain sensitive information about who can commit organizational resources. Without access controls, encryption, and audit logging, this data is vulnerable to manipulation — a risk that spreadsheet-based management cannot adequately mitigate.
- Manual oversight wastes time and money. The cumulative cost of manually maintaining signatory lists, chasing signature verifications, distributing updated lists to banking partners, and reconstructing authority records for auditors represents a significant operational burden. The APQC 2024 benchmarking data found that 75% of organizations using technology for delegation of authority management report it as effective, compared to only 64% of those without — an 11-percentage-point effectiveness gap attributable to manual process limitations.
What Effective Signatory Governance Looks Like
Moving from reactive signatory management to a structured governance model requires addressing people, process, and technology in concert — and the maturity progression below shows what that looks like in practice.
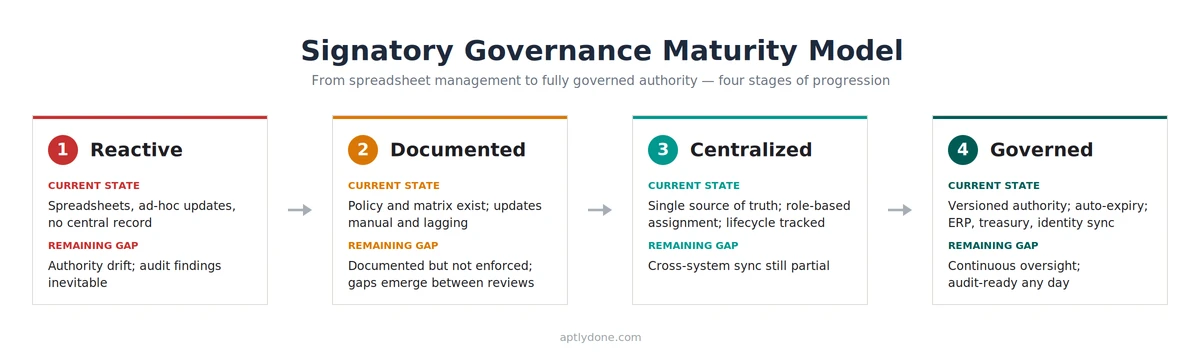
Organizations with mature signatory governance share several characteristics. Authority is tied to positions and roles rather than individuals, so personnel changes trigger automatic updates rather than manual list revisions. A centralized registry serves as the single source of truth, replacing the version-control chaos of distributed spreadsheets. Recertification happens on a defined cadence — quarterly or continuously — rather than waiting for audits or incidents to expose gaps. Distribution to counterparties and banking partners is digital and version-controlled, eliminating the risk that external parties hold outdated signatory records.
The EY/SCG 2025 survey found that 90% of organizations maintain a delegation of authority policy, but the gap between policy and practice is where risk lives. Having a policy that defines signatory authority is necessary but not sufficient — the governance infrastructure that enforces, monitors, and updates that authority in real time is what separates organizations that manage signatory risk from those that merely document it.
For organizations evaluating their signatory governance maturity, the critical question is not whether a policy exists, but whether the organization can answer — at any point in time, for any entity — exactly who has the authority to sign, under what conditions, and whether that authority is current.
Frequently Asked Questions
What is the difference between signatory authority and delegation of authority?
Delegation of authority defines who can approve decisions and commitments at specified financial and non-financial thresholds. Signatory authority defines who can execute those commitments by signing on behalf of the organization. The two must be aligned — a person should not hold signing authority for commitments they lack the approval authority to authorize.
How often should authorized signatory lists be reviewed?
Best practice is continuous maintenance triggered by personnel events (departures, role changes, restructurings), supplemented by a formal recertification at least quarterly. Organizations relying on annual reviews are exposed to authority drift for extended periods between review cycles.
What regulations require signatory governance controls?
SOX Section 302 (financial controls certification), the UK Corporate Governance Code (internal controls requirement), EU CSRD (governance disclosure), APRA CPS 510 in Australia (documented delegation frameworks for financial institutions), and various banking and securities regulations across jurisdictions all impose requirements that touch signatory governance.
What happens when an authorized signatory leaves the company?
Their signing authority must be revoked immediately across all internal records, banking mandates, and counterparty notifications. Any delay creates a window in which the departed individual can still legally bind the organization. This is one of the most common signatory governance failures and a frequent audit finding.
Why 2025–2026 is the regulatory inflection point
The regulatory environment that makes signatory governance auditable and accountable is converging on board agendas now. The UK Corporate Governance Code’s revised Provision 29, requiring boards to monitor the effectiveness of risk management and internal control systems, applies to financial years beginning on or after 1 January 2026. SOX modernization guidance is extending the scope of internal control attestation. The EU’s Corporate Sustainability Reporting Directive is mid-rollout across its 2024–2028 phased schedule, with governance disclosures that touch authority frameworks. The EU AI Act’s high-risk system provisions take effect in August 2026, embedding human-oversight requirements that directly intersect signatory authority. Each milestone independently raises the bar; together they make signatory governance auditable in ways most organizations are not yet ready for.
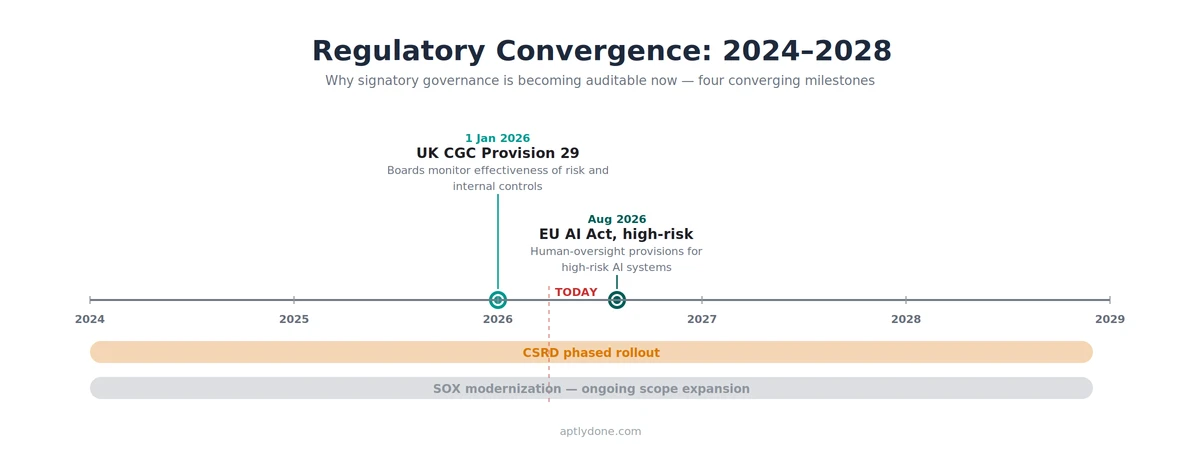
Governance leaders facing this convergence have a 12-month window to close the gap between policy and practice. Three actions create the foundation: audit current state to surface where signatory records, banking mandates, and counterparty distributions diverge from the policy of record; centralize authority records in a single registry that ties signing rights to positions and roles rather than individuals; and automate the lifecycle so that personnel events and recertification cycles update records without manual intervention. The eGRC market reflects the urgency — Grand View Research estimates the global market growing from $62.92 billion in 2024 to $134.86 billion by 2030, a 13.2% CAGR.
Sources
- EY and Society for Corporate Governance, The Delegation Edge: A Guide to Successful Delegation and Authority, January 2025.
- Association of Certified Fraud Examiners (ACFE), 2024 Report to the Nations, 2024.
- APQC, Delegation of Authority Policy Practices: Cross-Industry, 2024.
- Grand View Research, Enterprise Governance, Risk And Compliance Market To Reach $134.86Bn By 2030, February 2025.

