How to prevent misalignment between approval authority and execution authority - especially across multiple legal entities, bank accounts, and contract types.
For a primer on what signatory lists are and why they fail, see Authorized Signatory Lists Explained.
Definition: Authority alignment is the practice of ensuring that approval authority (who can approve a commitment), execution authority (who can sign or execute it), and system entitlements (who has access to perform the action) remain consistent across all organizational systems and counterparty records.
One of the most common quiet risks in enterprise authority programs is misalignment between approval authority and execution authority. Organizations often control approvals better than signatures, until they discover counterparties, banking partners, or contract management systems have different views of who can actually sign. A 2025 EY and Society for Corporate Governance study found that 65 percent of organizations centralize signatory authority within their delegation of authority policy, while 28 percent maintain entirely separate policies, creating immediate alignment challenges between the two.
Misalignment occurs because approval authority, execution authority, and system access are typically managed by different teams, in different systems, on different update cycles.
The root cause is structural: approval authority lives in a delegation of authority matrix, signatory authority lives in signatory lists or bank mandates, and system entitlements live in ERP, banking, and contract platforms. Each is maintained independently, and none automatically knows when the others change.
Several patterns show up repeatedly across organizations:
The EY/SCG study quantified these challenges directly: 35 percent of organizations report difficulty tracking and enforcing their DOA policy, 28 percent cite time-consuming update processes, and 27 percent struggle to maintain current versions due to rapid organizational changes. When approval authority and execution authority are governed separately, these challenges compound across every legal entity and bank account in the organization.
A 2024 APQC survey of 311 finance professionals reinforced this finding: 37 percent of organizations review their delegation of authority only on an ad-hoc basis, with an additional three percent rarely or never reviewing it. When review cadences are irregular, authority records drift out of alignment with actual organizational structures.
Enterprise authority operates across three distinct layers that must remain aligned: approval authority defines who can authorize a commitment, execution authority defines who can formally bind the organization, and system entitlements define who can physically perform the action in a platform.
Definition: Authority drift is the gradual divergence between approval authority, execution authority, and system entitlements that occurs when these three layers are updated on different schedules by different owners.
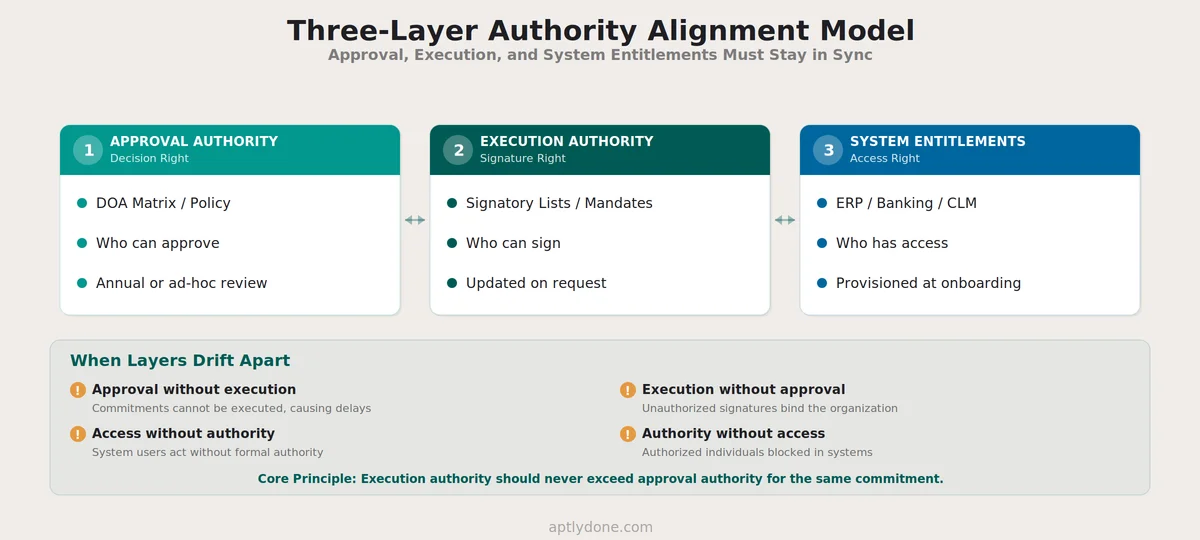
The table below breaks down each authority layer, what it controls, where it typically lives, and how it drifts out of alignment.
When these three layers diverge, organizations experience the full range of authority failures: people who can approve but cannot execute, people who can execute but should not be able to, and people who have system access without any formal authority for what they are doing. The APQC 2024 research found that 37 percent of organizations with ineffective delegation policies report inefficient use of resources as the top impact, and 30 percent cite a lack of accountability, both of which are direct consequences of authority layer misalignment.
Build reconciliation between these three layers into your operating cadence. A monthly check comparing delegation records to signatory lists to system entitlements, even for a sample of high-risk roles, catches drift before it creates incidents. For the systems integration perspective on drift prevention, see Avoiding Sync Drift: Keeping Authority Consistent Across Systems.
Authority misalignment carries measurable financial, operational, and compliance costs that compound across every entity where approval and execution authority diverge.
The financial exposure is significant. McKinsey research estimated that ineffective decision-making costs a typical Fortune 500 company approximately $250 million per year in wasted labor alone, with managers spending 37 percent of their time on decisions and 58 percent of that time used ineffectively. When authority misalignment forces re-approvals, escalations, and manual reconciliation, those costs accelerate.
Compliance costs are equally stark. A 2017 Ponemon Institute study found that the average cost of non-compliance reached $14.82 million, compared to $5.47 million for maintaining compliance, a 2.71 times multiplier that makes alignment failures one of the most expensive categories of preventable governance risk.
The ACFE's 2024 Report to the Nations found that 32 percent of occupational fraud cases stemmed from a lack of internal controls, and an additional 19 percent involved the override of existing controls. Misaligned authority creates exactly this gap: when execution authority exists without corresponding approval authority, it becomes an uncontrolled pathway for unauthorized commitments.
Organizations that close this gap see measurable improvement. The APQC 2024 study found that 67 percent of organizations with effective delegation policies report better decision-making, 62 percent report increased productivity, and 49 percent report a reduction in bottlenecks. The West Monroe Speed Wins report (2026) found that 73 percent of C-suite executives estimate that halving decision-making time would unlock at least five percent revenue growth, yet 44 percent of managers have accepted slow decision-making as normal within their organizations.
Effective authority alignment starts with a clear principle: execution authority should never exceed approval authority for the same commitment, and the system should be able to prove the approval chain for any signed instrument.
Three questions anchor every alignment framework:
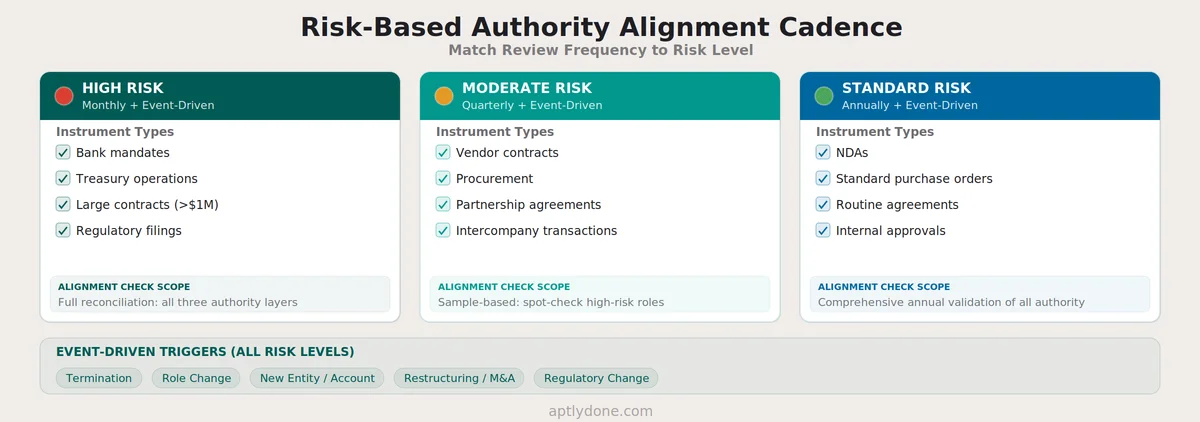
Risk-based alignment cadence ensures that review frequency matches the risk profile of each authority category. The table below outlines recommended review frequencies by instrument type and risk level.
The most effective way to keep delegations and signature authority in sync is to connect the systems where authority is defined to the systems where authority is exercised, creating automated alignment that does not depend on manual reconciliation.
Consider the lifecycle of a role change. When an employee is promoted from a regional controller to a divisional CFO, the following authority updates must happen:
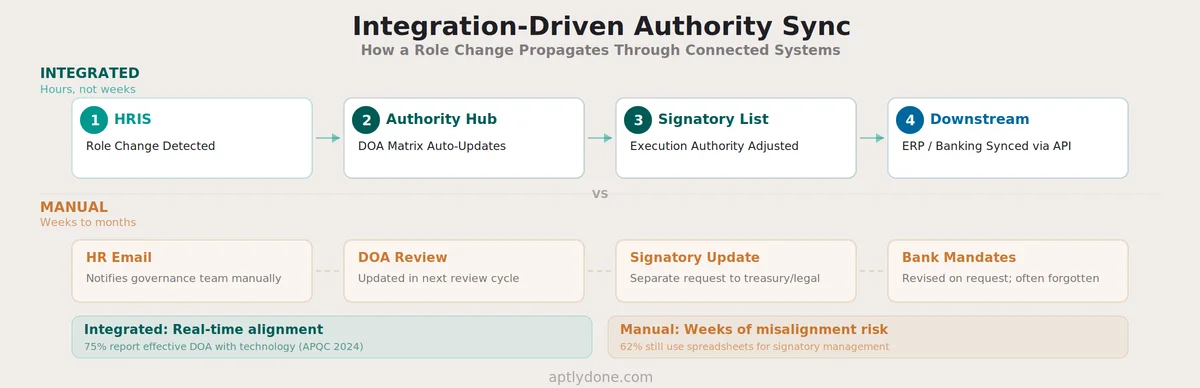
Without integration, each of these steps is a manual process handled by a different team on a different timeline. The EY/SCG 2025 study found that 78 percent of organizations host their DOA policy on the company intranet rather than in a dedicated system, and only 14 percent embed their DOA within a dedicated IT system for tracking and enforcement. This means the vast majority of organizations rely on manual processes to propagate authority changes across systems.
A 2021 industry report on signatory management found that 62 percent of organizations still use spreadsheets to manage signatory records, and the average time to update a signatory list is three or more weeks. When combined with the EY finding that 27 percent of organizations struggle to keep authority current with rapid organizational changes, the case for integration-driven alignment becomes clear.
The table below illustrates how integration-driven authority management transforms the manual alignment process into an automated chain.
The APQC 2024 research found that 75 percent of organizations using technology for DOA management report their policy as effective, compared to only 64 percent of those without technology. Integration does not just save time; it measurably improves the effectiveness of the entire authority governance program.
Maintaining alignment between approval and execution authority requires a combination of policy controls, operational practices, and system design that reinforces consistency across every entity and account.
Treating signatory lists as static reference documents. Signatory lists that are created once and updated only when someone notices an error will always lag organizational reality. Effective signatory governance treats these lists as dynamic, system-managed records that update in response to organizational events.
Assuming the DOA policy covers signing authority. The EY/SCG 2025 study found that 28 percent of organizations maintain signatory authority as an entirely separate policy from the DOA. Even among the 65 percent that combine them, the specifics of who can sign which instruments for which entities often receive less rigor than the approval thresholds in the DOA matrix. Signing authority deserves the same precision as approval authority.
Granting broad signing authority to operational convenience roles. Organizations sometimes authorize a small group of individuals, often executive assistants or finance managers, to sign across all entity and instrument types for operational speed. This creates a concentration of execution authority that may far exceed any individual's approval authority, violating the core alignment principle.
Reconciling authority only during annual reviews. Annual reviews are insufficient for organizations with frequent personnel changes, entity restructuring, or high transaction volumes. The APQC 2024 research found that 37 percent of organizations review their DOA only on an ad-hoc basis. Event-driven and risk-based review cadences are more effective than calendar-based schedules alone.
Failing to scope authority to legal entities. Multi-entity organizations that use a single generic authority structure almost always have alignment gaps at the entity level. Authority must be scoped to the specific legal entity, bank account, and jurisdiction where it will be exercised.
Aptly serves as the central, governed system of record for both delegation of authority and signatory management, addressing the three-layer alignment problem by maintaining approval authority and execution authority within a single platform.
Key capabilities that support authority alignment include cascading delegation with entity-level scoping, effective dating with automatic expiration on temporary assignments, controlled issuance and revocation of signatory authority tied directly to delegation records, and a searchable, auditable record of every authority change with point-in-time recall.
When paired with pre-built integrations for HRIS platforms such as Workday, SAP SuccessFactors, and BambooHR, identity providers such as Okta and Microsoft Entra, and ERP systems such as SAP, Oracle, and NetSuite, Aptly automates the authority change chain: a role change in HRIS triggers delegation updates, which flow to signatory list adjustments, which propagate to connected execution systems. This integration-driven approach replaces the manual, multi-week update process that creates misalignment in the first place.
The EY/SCG 2025 study found that 71 percent of organizations plan to invest in technology to improve their delegation of authority management. Purpose-built authority management platforms deliver this improvement by ensuring that approval authority and execution authority remain aligned by design, not by periodic manual reconciliation.
Independent ownership. When one team owns the DOA matrix and a different team owns signatory lists with no systematic reconciliation, the two inevitably drift. The fix is not necessarily merging ownership, but establishing a shared system of record and a regular alignment check between the two. The EY/SCG 2025 study found that 65 percent of organizations centralize signatory authority within their DOA, but even among those, the operational details of who can sign which instruments for which entities often receive less rigor than approval thresholds.
Scope every authority grant to specific legal entities. Use a single authority platform that supports entity-level rules, and ensure signatory lists and bank mandates explicitly reference entity scope. Multi-entity organizations that use a single generic authority structure almost always have alignment gaps at the entity level. Each subsidiary, branch, or joint venture should have its own authority profile derived from the parent DOA policy but tailored to its regulatory environment and operational requirements.
Not necessarily. Some organizations use operational signers who execute after approvals are documented, meaning signing authority is narrower than approval authority. The key principle is that execution authority should never exceed approval authority for the same commitment, and the system should be able to prove the approval chain for any signed instrument.
Monthly for high-risk instruments such as banking authorities and large-value contracts, quarterly for moderate-risk categories, and at minimum annually for all authority. Event-driven checks should trigger on every termination, role change, new entity creation, and organizational restructuring. The APQC 2024 study found that 37 percent of organizations review their DOA only ad-hoc, which is insufficient for maintaining alignment.
Definition: Approval authority (decision right) is the organizational permission to authorize a commitment. Execution authority (signature right) is the legal authority to bind the organization by signing an instrument. A regional VP may approve a vendor contract up to $500,000 (approval authority), but the CFO or General Counsel may be the only person authorized to actually sign it (execution authority).
When execution authority exists without corresponding approval authority, it creates an uncontrolled pathway for unauthorized commitments. The ACFE's 2024 Report to the Nations found that 32 percent of occupational fraud cases stemmed from a lack of internal controls and 19 percent involved override of existing controls. Authority misalignment is a form of control gap that auditors specifically look for under SOX and internal control frameworks.
Technology significantly reduces misalignment but cannot eliminate it entirely. The APQC 2024 research found that 75 percent of organizations using technology for DOA management report their policy as effective, compared to 64 percent without technology. Integration-driven alignment automates routine updates, but policy design decisions, exception handling, and organizational judgment still require human governance.
Five event types should trigger immediate review: employee termination or resignation, role change or promotion, creation of a new legal entity or bank account, organizational restructuring or M&A activity, and changes to regulatory requirements affecting authority thresholds. Each of these events can create misalignment between approval and execution authority if not addressed promptly.
Require every temporary signing authority assignment to carry explicit effective dates and automatic expiration. Document the scope limitations, including entity, instrument type, and monetary threshold. Ensure the temporary authority is reflected in both the delegation record and the signatory list simultaneously, and confirm revocation through system audit trail when the temporary period ends.
The DOA matrix defines approval authority, the upstream control that should govern who receives execution authority. When the DOA matrix is the canonical source of authority rules, signatory lists become a governed downstream output. Changes to the matrix, such as updated thresholds, new authority categories, or organizational restructuring, should trigger corresponding updates to signatory records.
Connect with our team for a discovery session to learn more about how Aptly can help within your organization. If you are already a client and need support, contact us here.