
A clear explanation of authorized signatory lists, how they relate to delegation of authority, and why outdated lists create operational and fraud risk.
Definition: An authorized signatory list — also known as an authorised signatory list in international banking and regulatory contexts — is a governed record of individuals permitted to execute specific instruments, such as contracts, banking instructions, board resolutions, and corporate filings on behalf of the organization, typically scoped by legal entity, instrument type, and signing threshold.
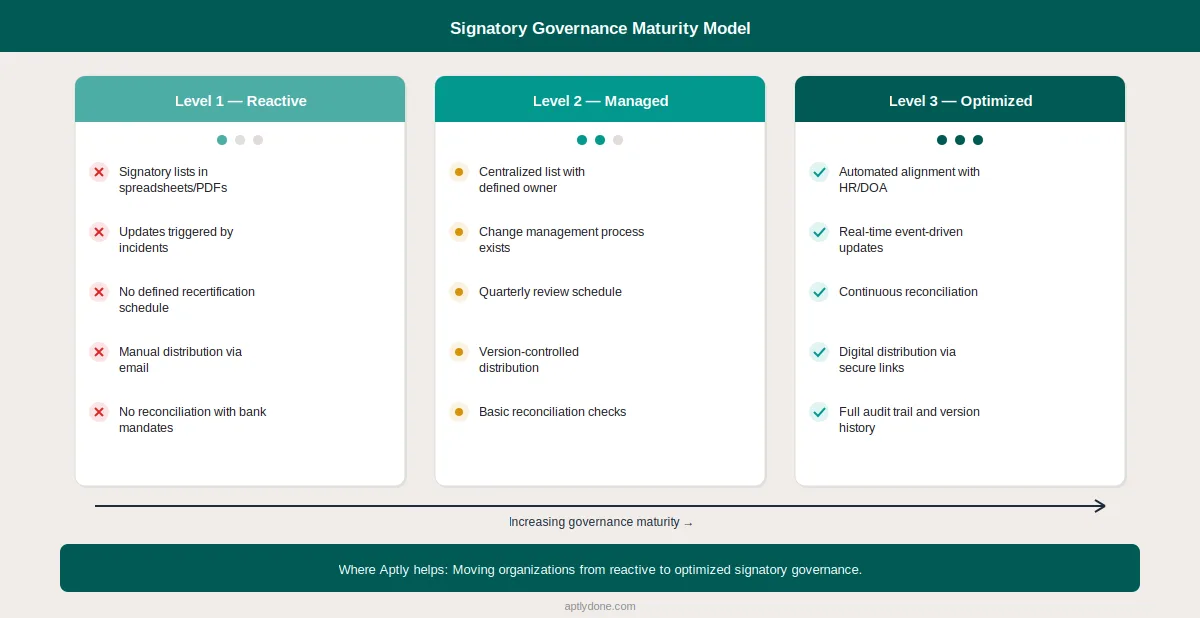
Authorized signatory lists sound simple: a list of people who can sign on behalf of the organization. In reality, they become complex quickly — especially across entities, bank accounts, and contract types. Research consistently shows that most organizations still manage signatory lists using spreadsheets, PDFs, and email — creating operational risk that grows with every entity added and every role change left unprocessed. A University of Hawaii meta-analysis of spreadsheet audits found that 88 percent of spreadsheets contain errors, with logic errors accounting for roughly four out of five mistakes — meaning authority records maintained in spreadsheets inherit that error rate across every governance decision.
This guide explains what authorized signatory lists should contain, how they relate to the delegation of authority, why they break down over time, and what a mature governance program looks like in practice.
An authorised signatory list is a formal document that records which individuals have the authority to execute legally binding instruments on behalf of an organization, including the specific conditions and limits under which that authority applies.
Definition: An authorized signatory is an individual formally designated by an organization to execute legally binding instruments on its behalf, typically through board resolution, power of attorney, or delegation of authority grant.
The list itself is not a legal instrument — it is a governance record that reflects the authority granted through other instruments (board resolutions, corporate bylaws, powers of attorney). Its purpose is operational: ensuring that the right people can sign the right things, and that everyone who needs to know — banks, counterparties, auditors, internal teams — has access to the current, accurate version.
An authorized signatory list is not the same thing as several related governance concepts. The comparison below clarifies the distinctions that matter in practice.
Good governance makes these concepts align. Operational reality often does not. A 2013 Deloitte study on governance operating models found that organizations with clearly defined accountability structures — including explicit signatory governance — reduce operational risk by maintaining consistent oversight across all three lines of defense.
A complete authorized signatory list captures identity, scope, limits, validity, and supporting documentation for every individual authorized to sign on behalf of the organization — ensuring that every signatory entry can be independently validated.
Definition: Signing authority is the scope of instruments, monetary values, and conditions under which an authorized signatory may execute documents on behalf of the organization.
Most signatory lists fail because they capture only names and titles. A governed list needs to answer six questions for every entry: who is authorized, what can they sign, up to what value, for which entity, under what conditions, and until when?
The table below shows the essential fields every authorized signatory list entry should include.
The 2025 EY-Society for Corporate Governance study found that 33 percent of organizations lack a formal delegation-of-authority framework — and those organizations are also less likely to maintain complete signatory records, since the foundational policy that defines who can approve and sign is missing.
Signatory lists degrade through three failure modes: role changes that are not reflected in the list, organizational changes that create entity-level gaps, and decentralized management that produces conflicting versions.
Definition: Signatory drift is the gradual divergence between formal signatory records and the actual authority exercised within an organization, typically caused by unprocessed role changes, entity restructurings, and decentralized list management.
Understanding why signatory lists fail requires looking beyond individual errors to the systemic conditions that produce them.
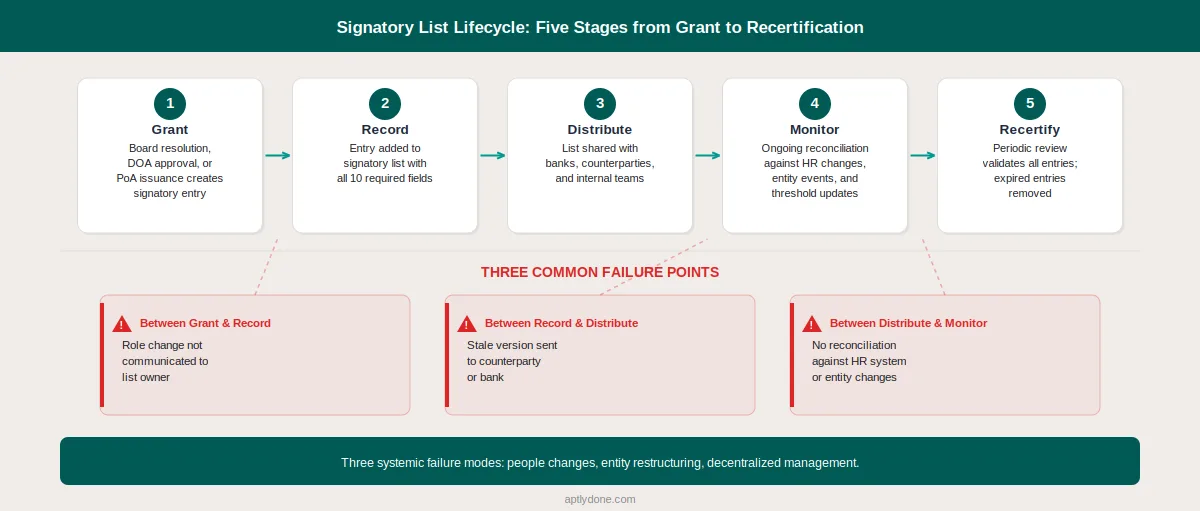
Every role change, termination, and new hire creates a potential signatory update. In most organizations, these updates depend on manual notifications — HR tells Legal, Legal updates the list, Treasury notifies the bank. Any break in this chain leaves stale entries on the signatory list. The 2024 ACFE Report to the Nations found that 5 percent of organizational revenue is lost to fraud annually — a figure that includes losses from unauthorized transactions that exploit gaps in signatory governance.
Mergers, acquisitions, divestitures, and new entity formations create immediate signatory governance challenges. The acquired entity has its own signatory lists, usually in different formats with different threshold structures. Until those lists are consolidated and standardized, the organization operates with inconsistent authority controls. A McKinsey study on organizational decision-making found that top-quartile decision-making organizations make decisions 2× faster and 3× more effectively — but this requires the governance infrastructure (including signatory lists) to keep pace with structural changes.
When multiple teams maintain separate signatory lists for different purposes — one for banking, one for contracts, one for corporate filings — divergence is inevitable. Without a single source of truth, each list evolves independently, creating contradictions. The counterparty checking the banking authorised signatory list sees different authority than the legal team reviewing the contract signatory list for the same person.
Broken signatory lists create three categories of measurable cost. Transaction delays occur when banks or counterparties reject signatures from individuals whose authority is not current on the signatory list. Compliance exposure arises when auditors find that actual signing practices do not match documented authority. Fraud risk increases when former employees or unauthorized individuals remain on active signatory lists.
The numbers reinforce the risk. The FBI's 2024 Internet Crime Report recorded over $16.6 billion in reported cybercrime losses, with business email compromise (BEC) accounting for a significant share — and BEC attacks specifically target signatory and payment authorization processes. The 2025 AFP Payments Fraud and Control Survey found that 65 percent of organizations experienced attempted or actual payments fraud in 2024 — with checks and ACH credits as the most targeted payment methods, both of which depend on signatory controls. Separately, Fenergo reports that financial institution fines surged to $4.6 billion in 2024, and KYC compliance fines jumped 102 percent in the first half of 2024 alone — both trends underscore how regulators are intensifying enforcement around identity verification and authority controls.
The digital signature market is growing accordingly. Fortune Business Insights projects the market will reach $43.1 billion by 2030, reflecting the accelerating shift from manual to digital signatory processes across industries. The keeping delegations and signature authority in sync guide provides a detailed approach to preventing this drift.
A governed signatory program requires four components: a defined scope, clear ownership, an update process that connects to HR and entity changes, and a reconciliation mechanism that detects drift.
Start by mapping every instrument type that requires a signature: contracts, banking transactions, board resolutions, corporate filings, tax documents, regulatory submissions. For each type, identify which entities are in scope and what the current signing rules are. This mapping typically reveals gaps — instrument types that have no formal signatory governance.
Every signatory entry should capture the ten fields listed in the table above. Standardizing the format across all entities and instrument types makes the list auditable and enables automated reconciliation. The DOA vs. Approval Matrix vs. RACI comparison can help clarify how signatory lists relate to other governance tools.
Define the events that require a signatory list update: new hires, role changes, terminations, entity formations, M&A events, threshold changes, and periodic reviews. For each trigger, specify who initiates the update, who approves it, and what the target turnaround time is. The authority change management playbook provides a detailed approach to building reliable update processes.
Scheduled reconciliation between the signatory list and downstream systems (bank mandates, contract management platforms, e-signature tools) catches drift before it causes operational failures. The authority monitoring and reporting metrics guide defines the KPIs that indicate whether your signatory governance is functioning as designed.
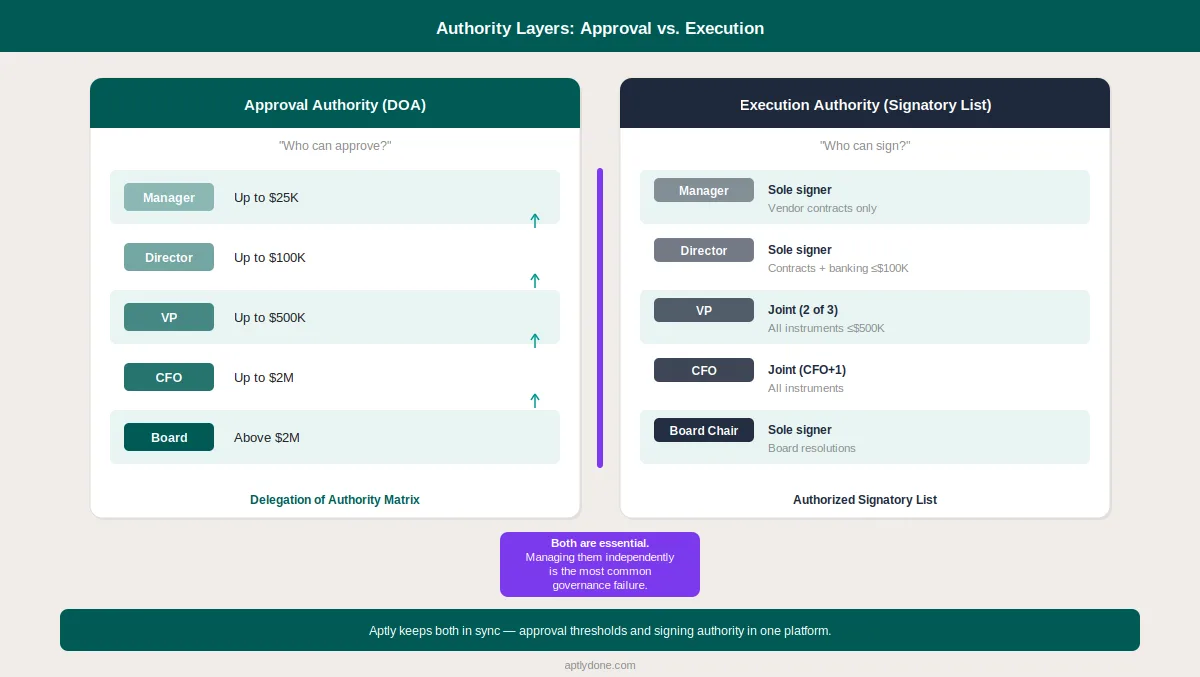
The signatory list and the delegation of authority are separate documents that must stay aligned. When a DOA threshold changes, the corresponding signatory limits should be reviewed. When a new approval level is created, the signing authority for that level should be defined. A DOA policy that people actually follow reduces the governance gap between what is approved and what is signed.
Organizations with mature signatory governance share five characteristics: centralized records, real-time updates triggered by HR events, automated reconciliation with banks and counterparties, version-controlled audit trails, and digital distribution that eliminates stale PDF copies.
The 2026 West Monroe Speed Wins study found that slow organizational decision-making costs the average large enterprise $250 million per year in lost productivity — and signatory bottlenecks are a material contributor to those delays when the wrong person is listed or the right person's authority has expired.
Aptly's signatory management module provides a centralized, version-controlled signatory list with real-time updates, digital distribution, and integration with the broader delegation of authority. The single source of truth through authority integrations guide explains how signatory data can be synchronized across the systems that depend on it.
At minimum, quarterly — with immediate updates triggered by role changes, terminations, and entity restructurings. Organizations with high transaction volumes or complex entity structures should review monthly. The critical factor is not the review frequency but the speed of event-driven updates: a list that is reviewed quarterly but takes three weeks to process a termination still has a governance gap.
A bank mandate is the formal instruction to a bank specifying who can operate an account — it is a subset of the broader signatory list focused specifically on banking transactions. The signatory list covers all instrument types (contracts, filings, resolutions), while the bank mandate covers only bank account operations. In practice, the signatory list and bank mandates often drift apart — creating a risk that the bank recognizes signatories the organization has internally revoked.
Typically, Treasury or Legal owns signatory lists for banking and corporate instruments, while Procurement or Legal Operations owns contract signing authority. The critical factor is that a single function has clear ownership for each instrument type, with a defined update process that connects to HR role changes and DOA updates. Split ownership across multiple teams without reconciliation is the single most common cause of signatory list failures.
Immediate actions should include revoking the individual's signing authority across all lists and systems, notifying banks and counterparties of the removal, updating internal signatory records, reviewing any pending transactions requiring that individual's signature, and activating pre-approved backup signatories if coverage gaps exist. The speed of this process is a key indicator of signatory program maturity — organizations operating on spreadsheets typically take three or more weeks to complete these steps.
Yes, and digital distribution is increasingly the standard. Banks and counterparties need to verify signing authority before processing transactions, and secure digital sharing eliminates the version confusion inherent in emailing PDFs. The best approach uses controlled, version-tracked links — so recipients always access the current list rather than a static snapshot that may be outdated. Aptly supports this through secure sharing links with version history.
Sole signing authority allows one individual to execute an instrument independently. Joint signing authority requires two or more co-signatories. Most organizations use threshold-based rules: sole signing for lower-value transactions and joint signing above a defined monetary limit. The signatory list must specify which combination applies to each signatory for each instrument type — otherwise, the list is ambiguous and counterparties may reject transactions.
Both spellings are correct and refer to the same governance concept. "Authorized" follows American English convention, while "authorised" is the standard spelling in British English, Australian English, and most international regulatory frameworks — including FCA, APRA, MAS, and EU directives. Banks and counterparties in the UK, Europe, Asia-Pacific, and the Middle East typically use "authorised signatory" and "authorised signatory list" in their mandate documentation. The legal meaning, governance requirements, and operational best practices are identical regardless of spelling convention.
Mergers and acquisitions create immediate signatory governance challenges. The acquired entity brings its own signatory lists, often in different formats with different thresholds and approval logic. Integration requires consolidating lists across entities, standardizing fields and thresholds, updating bank mandates for merged accounts, revoking authorities for departed executives, and establishing signing authority for new leadership. Organizations that delay this consolidation operate with parallel governance structures that increase fraud exposure.
Signatory lists intersect with multiple regulatory frameworks. SOX Section 404 requires documentation of internal controls over financial reporting — which includes signatory governance. KYC and AML regulations require financial institutions to verify authorized signatories. The EU's eIDAS regulation defines three levels of electronic signatures (simple, advanced, and qualified) that affect how digital signatory authority is documented. GDPR applies to the personal data contained within signatory lists, particularly specimen signatures and identification documents. For more on SOX compliance specifically, see DOA and SOX Internal Controls.
A delegation of authority matrix defines who has the power to approve decisions and commitments at various thresholds — it governs decision rights. An authorized signatory list defines who can execute those approved commitments by signing instruments — it governs execution rights. The DOA answers "who can approve this $500,000 contract?" while the signatory list answers "who can sign it?" Both are essential, and the most common governance failure is managing them independently without reconciliation. See Delegation of Authority 101 for a comprehensive overview.
Multi-entity signatory governance requires a centralized record that tracks authority at the entity level while maintaining a consolidated view across the group. Each entity should have its own signatory list (because authority is granted per entity), but a central function should have visibility across all lists to identify gaps, overlaps, and inconsistencies. The PwC 2024 Global Economic Crime Survey confirms that compliance requirements have grown significantly more complex in recent years — multi-entity signatory management is one of the areas where that complexity is most acute.
Connect with our team for a discovery session to learn more about how Aptly can help within your organization. If you are already a client and need support, contact us here.