Managing the Risks Associated with Authorized Signatories
Authorized signatories or signers are individuals who have the legal power to bind an organization to contracts, agreements, or transactions. They are often senior executives, board members, or authorized representatives of the organization. Managing authorized signatories is a critical governance function for any business, as it involves ensuring that the right people have the right level of authority, and that signatory records are accurate, current, and compliant with applicable laws and regulations.
Poor signatory governance exposes organizations to unauthorized transactions, compliance failures, and financial losses — risks that intensify as enterprises scale across entities, jurisdictions, and digital signing platforms.
However, managing authorized signatories is not without risks. There are many potential pitfalls that can result in serious consequences, including financial losses, legal liabilities, reputational damage, and regulatory sanctions. According to the Association of Certified Fraud Examiners (ACFE), organizations lose an estimated 5% of annual revenue to fraud, with a median loss of $145,000 per case — and 89% of occupational fraud cases involve asset misappropriation, which includes check tampering and payment fraud where signatory controls are a direct mitigation.
In this article, we discuss the top five risks associated with managing authorized signatories, and practical strategies for addressing each one. For a deeper understanding of what authorized signatory lists are and how they function, see our comprehensive guide to authorized signatory lists explained.
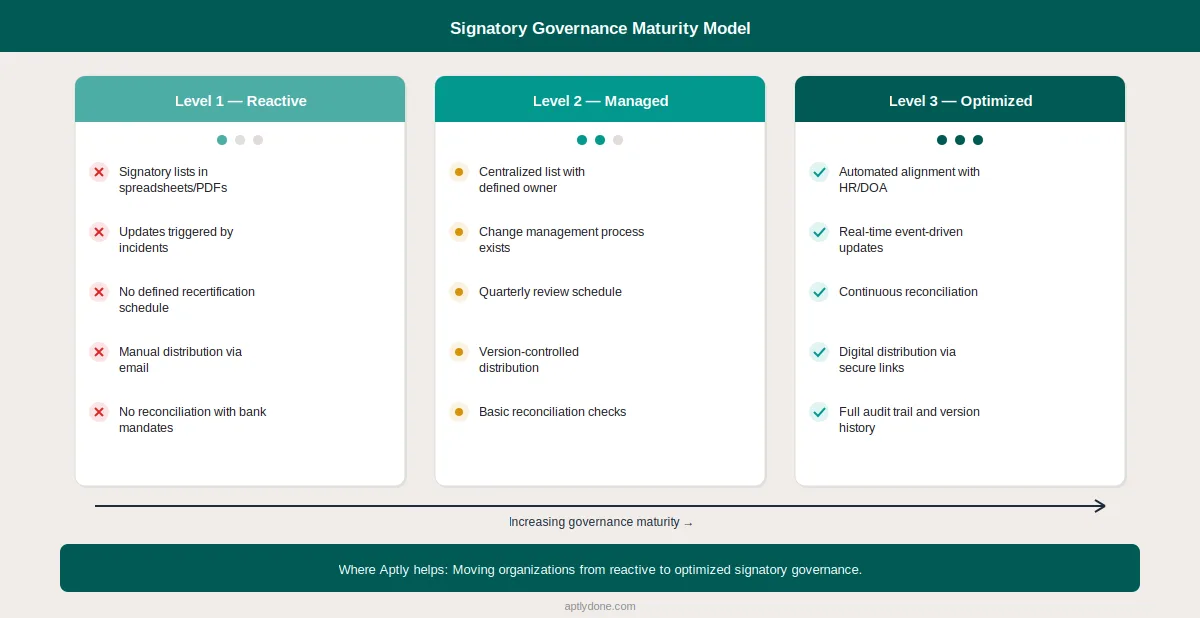
Most organizations fall somewhere on a signatory governance maturity spectrum — from reactive environments where lists are managed ad hoc in spreadsheets with no audit trail, to optimized programs with automated HR-triggered updates, real-time DOA alignment, and continuous recertification. The five risks outlined below disproportionately affect organizations operating at the reactive end of that spectrum.
The Five Critical Risks of Authorized Signatory Management
Risk 1: Unauthorized or Fraudulent Signatures
One of the most obvious and serious risks is that someone who is not authorized to sign on behalf of the organization does so, either by mistake or with malicious intent. This can happen when signatory records are not updated regularly, when the verification process is weak or nonexistent, or when signatory documents are not stored securely. Unauthorized or fraudulent signatures can expose the organization to unwanted obligations, disputes, lawsuits, or fines.
The scale of this risk is substantial. The FTC reported $12.5 billion in consumer fraud losses in 2024, a 25% increase over 2023. In the corporate context, the ACFE found that 87% of fraud perpetrators were first-time offenders with no prior history — meaning organizations cannot rely on background checks alone. Effective signatory controls are a frontline defense.
To prevent this risk, organizations should:
- Establish a clear and consistent policy defining who can sign which document types, under what monetary thresholds, and under what circumstances
- Maintain a centralized authorized signatory list as a single source of truth, updated whenever there is any change in signatory status
- Implement multi-party approval workflows that require sign-off before any signatory additions or changes take effect
- Conduct regular audits and reviews of signatory records and documents, and report any discrepancies immediately
For a step-by-step approach to addressing this risk, see our Q&A guide on preventing unauthorized signatures.
Risk 2: Inconsistent or Outdated Signatory Information
Another common risk is that signatory information is not consistent or current across different systems, platforms, or jurisdictions. This frequently occurs when organizations maintain multiple signatory databases that are not synchronized, or when signatory updates are not communicated in a timely manner across the enterprise.
Industry research consistently shows that the majority of organizations still rely on spreadsheets and static PDF documents to manage signatory information — and that it often takes weeks to update signatory lists after a single personnel change. During that gap, outdated signatory information creates a window of vulnerability where former employees may still appear as authorized signers, or new signatories may be unable to execute time-sensitive transactions.
The consequences are tangible: inconsistent signatory records cause confusion, delays, errors, and rejections in the signing process, and can affect the validity or enforceability of signed documents. Banks and counterparties often carry different "current" versions of signatory lists than internal teams, producing payment rejections, transaction delays, and emergency re-approvals.
To avoid this risk, organizations should have a single source of truth for signatory information that is accessible and accurate across all relevant systems, platforms, and jurisdictions. A standardized and automated update process — with notifications to all relevant parties including internal departments, external partners, and regulators — is essential. Understanding how delegations and signature authority stay in sync is critical for eliminating this gap.
Risk 3: Lack of Visibility or Control Over Signatory Activities
A third risk is that the organization lacks sufficient visibility or control over signatory activities — who is signing what, when, where, and why. This commonly occurs when signatory processes are manual or paper-based, when there is no centralized management system, or when reporting and analytics capabilities are inadequate.
The ACFE's 2024 Report to the Nations found that 51% of occupational fraud losses are enabled by either absent internal controls (32%) or management override of existing controls (19%) — the exact visibility and control gaps that signatory governance is designed to close. When authority is not properly administered, the organization is exposed to blind spots that can lead to inefficiencies, errors, fraud, or non-compliance.
To mitigate this risk, organizations need a robust and integrated signatory management system that can capture, store, manage, and analyze all signatory data and documents. Key capabilities include workflow automation, electronic signatures, alerts and notifications, comprehensive audit trails, and real-time dashboards. The system should enable organizations to streamline the signatory process, enhance security and compliance, and provide real-time visibility into who holds what authority at any given moment.
An effective system should also maintain complete version history — the ability to reproduce "who could sign as of any prior date" is increasingly important for both internal audits and regulatory examinations.
Risk 4: Inadequate Signatory Training and Support
A fourth risk is that signatories or signatory managers are not adequately trained or supported in their roles and responsibilities. This can happen when the organization lacks a clear signatory policy or procedure, when training is insufficient or outdated, or when support resources are unavailable.
This risk is compounded by scale. McKinsey research indicates that 60% of financial processes remain manual, meaning the people responsible for signatory governance are often juggling manual workflows alongside their training and compliance obligations. Without proper training, signatory errors, misunderstandings, and non-compliance multiply.
To overcome this risk, organizations should:
- Maintain a clear and comprehensive signatory policy that defines roles, responsibilities, processes, and requirements
- Provide regular training covering both the signatory system and tools as well as applicable laws and regulations
- Ensure that the delegation of authority policy is accessible and written so that people actually follow it
- Offer timely support that can address signatory queries, issues, and edge cases as they arise
Risk 5: Non-Compliance with Signatory Laws and Regulations
The fifth risk is that the organization fails to comply with the laws and regulations governing signatory authority, validity, or enforceability. This can occur when organizations are not aware of changing requirements, when implementation lags behind regulatory updates, or when compliance is not adequately documented.
The stakes of non-compliance continue to rise. According to Fenergo, financial crime fines exceeded $4.7 billion globally in 2024, with regulatory enforcement increasingly focused on inadequate internal controls — including authority management and signatory governance. For public companies, signatory controls also intersect directly with SOX Sections 302 and 404 requirements for internal controls over financial reporting.
To address this risk, organizations should be aware of and current on the signatory laws and regulations that apply to their industry, location, and operations. This includes implementing compliant signatory processes, ensuring documentation meets regulatory standards, and maintaining evidence of compliance through certificates, attestations, and audit trails.
The Three Layers of Authority That Must Stay Aligned
One often-overlooked dimension of signatory risk is the misalignment between different layers of authority within an organization. Effective signatory governance requires alignment across three distinct layers:
- Approval authority (Delegation of Authority): Who is authorized to approve a decision or commitment — defined by the delegation of authority framework
- Execution authority (Signatory rights): Who is authorized to sign and legally bind the organization to that commitment
- System entitlements (Access controls): Who has the system-level access to actually execute the transaction in ERP, banking, or procurement platforms
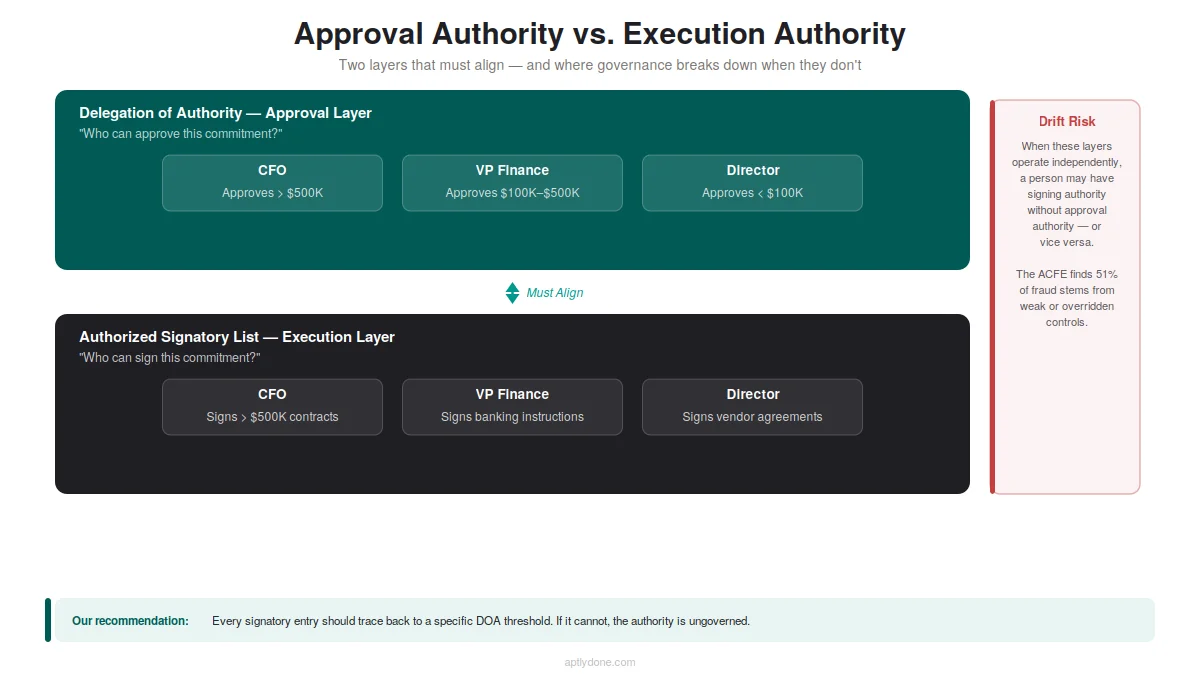
When these three layers fall out of sync — which happens frequently during personnel changes, reorganizations, or system migrations — the result is either unauthorized actions that bypass governance controls, or unnecessary bottlenecks where authorized individuals cannot execute decisions they have been empowered to make. For a deeper look at this alignment challenge, see our article on keeping delegations and signature authority in sync.
Conclusion: From Risk Management to Authority Governance
Managing authorized signatories is crucial for any organization that wants to avoid the risks and costs of signatory errors, delays, disputes, fraud, and non-compliance. By maintaining accurate signatory records, implementing proper controls, and ensuring real-time visibility into who holds what authority, organizations can protect themselves from financial, legal, and reputational harm.
However, managing authorized signatories effectively becomes increasingly challenging as organizations grow in size, complexity, and geographic reach — particularly as the transition from paper-based to digital signing continues to accelerate. Companies with streamlined authority and decision frameworks achieve 16% greater growth, according to McKinsey — making signatory governance not just a risk mitigation exercise, but a competitive advantage.
Aptly's signatory management platform provides a centralized, secure, and auditable system for managing authorized signatory lists across the enterprise. Organizations can create and update signatory records, define financial and non-financial authority limits, share signatory lists via secure links, and maintain comprehensive audit trails — all while ensuring real-time synchronization with delegated authority records. The result: reduced risk, improved compliance, and signatory governance that keeps pace with the organization.
Frequently Asked Questions
What is an authorized signatory?
An authorized signatory is a person who has been given the legal right to sign documents — such as contracts, agreements, or financial instruments — on behalf of an organization. Authorization is typically granted through a board resolution, delegation of authority framework, or power of attorney, and may be scoped by document type, monetary threshold, or legal entity.
What are the biggest risks of poor signatory management?
The five primary risks are unauthorized or fraudulent signatures, inconsistent or outdated signatory information, lack of visibility over signatory activities, inadequate training and support, and non-compliance with signatory laws and regulations. These risks can result in financial losses, legal liability, regulatory penalties, and reputational damage.
How often should authorized signatory lists be updated?
Authorized signatory lists should be updated immediately whenever there is a personnel change, role change, organizational restructuring, or change in authority limits. Best practice is to maintain a system that triggers updates automatically based on organizational events, rather than relying on periodic manual reviews. In many organizations, the lag between a personnel change and a signatory list update can stretch to weeks — a gap that creates significant exposure.
What is the difference between delegation of authority and signatory authority?
Delegation of authority (DOA) defines who is authorized to approve or commit to decisions within specified limits. Signatory authority defines who is authorized to execute — to physically or electronically sign — documents that give legal effect to those decisions. Both must be aligned and current to maintain effective governance. Learn more in our Delegation of Authority 101 guide.
How can technology help manage signatory risks?
Digital signatory management platforms replace manual spreadsheets and static PDF lists with centralized, real-time systems that automate updates, enforce approval workflows, maintain comprehensive audit trails, and enable secure sharing with internal and external stakeholders. This eliminates the delays, errors, and visibility gaps that create the majority of signatory risks.

